An Intelligent Method for Intrusion Detection and Prevention in Mobile AdHoc Networks
Keywords:
Encryption, Firewalls, Mobile AdHoc Network, Internet of Things, Intrusion Detection SystemAbstract
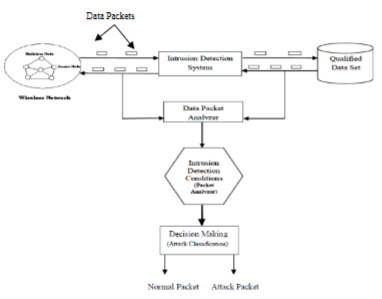
A Mobile ad hoc network (MANET) is a set of wireless multi-hop network which can broadcast data over an intermediate node; these networks have been universally used and become an essential since the expansion of the Internet of Things (IoT). However, the communications on MANET are sensitive, it mostly affected by several internal or external attackers, and the research on security issues of MANET is becoming most needed recently. Malicious nodes such as Black hole attack are one of the most prominent attacks in MANET. The conventional technique for firewalls and encryption is not sufficient for securing the system. Hence an intrusion detection system must be implemented in the mobile ad hoc network. One of the various types of misbehavior a node may exhibit is selfishness. Indiscipline or selfish node wishes to preserve their resources when using the services of others and utilizing their resources. Malicious nodes that violate regulations and decrease the performance of well-behaved nodes automatically. One method for protecting selfishness in a MANET is a find and isolates method. This paper, describes a different method for detecting malicious nodes in mobile ad hoc networks with the design of Intrusion Detection and prevention schemes for improving the security of MANET. This paper proposes a dynamic algorithm for identifying malicious presence in a MANET environment and conduct experiments to check algorithm efficiency with other algorithms.
Downloads
References
M.Arulselvan, S.Selvakumar, Malicious node identification using quantitative intrusion detection techniques in MANET.Springer Science +Business Media,LLC,part of Springer Nature 2018,http://doi.org/10.1007/s10586-018-2418-2.
M.Islabudeen,M.K.Kavitha Devi, A Smart Approach for Intrusion Detection and Prevention System in Mobile Ad Hoc Networks Against Security Attacks. Springer Science +Business Media, LLC, part of Springer Nature 2020, http://doi.org//10.1007/s11277-019-07022-5.
A.R.Rajeswari,K.Kulothungan et.al, Trust Aware Svm Based Ids For Mitigating The Malicious Nodes In Manet,International Journal of Innovative Technology and Exploring Engineering(IJITEE) ISSN:2278,Volume-8 Issue-8,June,2019.
Kuldeep Singh,Karandeep Singh, Intrusion Detection and Recovery of MANET by using ACO Algorithm and Genetic Algorithm, Springer Nature Singapore pte Ltd.2018,Next-Generation Networks,Advances in Intelligent Systems and Computing 638, http://doi.org/10.1007/978-981-10-6005-2_11.
Mohamed Assia ,Abdelfettah Belghith,5 th International Conference on Ambient Systems, Networks and Technology(ANT-2014),A node quality based clustering algorithm in wireless mobile Ad Hoc networks,doi:10.1016/j.procs.2014.05.412.
Jan PAPAJ, Lubomir DOBOS, Trust Based Algorithm for Candidate Node Selection in Hybrid MANET-DTN, Information and Communication Technologies and Services Volume 12, Number: 4, 2014, Special Issue.
Garg, D. K. . (2022). Understanding the Purpose of Object Detection, Models to Detect Objects, Application Use and Benefits. International Journal on Future Revolution in Computer Science &Amp; Communication Engineering, 8(2), 01–04. https://doi.org/10.17762/ijfrcsce.v8i2.2066
Hiral Vegda,Dr.Nimesh Modi, Secure and Efficient Approach to Prevent Ad hoc Network Attacks using Intrusion Detection System,Second International Conference on Intelligent Computing and Control System(ICICCS 2018) IEEE Xplore,ISBN:978-1-5386-2842-3.
Panagiotis I.Radoglou et al.Flow Anomaly Based Intrusion Detection System for Android Mobile Devices, 2017 6 th International Conference on Modern Circuits and Systems Technologies (MOCAST).978-1-5090-4386-6/17.
Spana B.Kulkarni,B.N.Yuvaraju, Trust Value Updation Algorithm for Multicast Routing Algorithm for Cluster Based MANET ,IEEE WiSPNET 2017 conference,978-1-5090-4442-9/17,IEEE.
Masood Ahmad,Abdul Hameed et al. A bio-inspired clustering in mobile adhoc networks for internet of things based on honey bee and genetic algorithm,Journal of Ambient Intelligence and Humanized Computing, http://doi.org//10.1007/s12652-018-1141-4.
Garg, D. K. . (2022). Understanding the Purpose of Object Detection, Models to Detect Objects, Application Use and Benefits. International Journal on Future Revolution in Computer Science &Amp; Communication Engineering, 8(2), 01–04. https://doi.org/10.17762/ijfrcsce.v8i2.2066
Yi Yi Aung ,Myat Myat Min, A Collaborative Intrusion Detection Based on K-means and Projective Adaptive Resonance Theory,2017 13 th International Conference on Natural Computation, Fuzzy Systems and Knowledge Discovery(ICNC-FSKD 2017) 978-1-5386-2165-3/17,IEEE.
Khondekar Lutful Hassan,Somnath Bera et al. Agent Based IDS Using RMBOPB Techniques in MANET,Springer Nature Singapore Pte Ltd.2017,DOI:10.1007/978-981-10-6427-2_28.
Preeti Pandey,Atul Barve, An Energy – Efficient Intrusion Detection System for MANET. Springer Nature Singapore Pte Ltd.2019.https://doi.org/10.1007/978-981-13-6351-1_10.
Prasanthi Sreekumari, Implementation of an Acknowledgment and Signature based Intrusion Detection System for MANETS. Springer Nature Switzerland AG2019. International Conference on Information Technology-Next Generations (ITNG 2019) Advances in Intelligent Systems and Computing. https://doi.org/10.1007/978-3-030- 14070-0_92.
Garg, D. K. . (2022). Understanding the Purpose of Object Detection, Models to Detect Objects, Application Use and Benefits. International Journal on Future Revolution in Computer Science &Amp; Communication Engineering, 8(2), 01–04. https://doi.org/10.17762/ijfrcsce.v8i2.2066
D.Muruganandam, J.Martin Leo Manickam, An efficient technique for mitigating stealthy attacks using MNDA in MANET, The Natural Computing Applications Forum2018. https://doi.org/10.1007/s00521-018-3634-7.
Garg, D. K. . (2022). Understanding the Purpose of Object Detection, Models to Detect Objects, Application Use and Benefits. International Journal on Future Revolution in Computer Science &Amp; Communication Engineering, 8(2), 01–04. https://doi.org/10.17762/ijfrcsce.v8i2.2066
K.Bala,S.Jothi et al. An enhanced intrusion detection system for mobile ad-hoc Network based on traffic analysis,Springer Science +Business Media,LLC,part of Springer Nature 2018. https://doi.org/10.1007/s10586-018-25459.
Paithane, P. M., & Kakarwal, D. (2022). Automatic Pancreas Segmentation using A Novel Modified Semantic Deep Learning Bottom-Up Approach. International Journal of Intelligent Systems and Applications in Engineering, 10(1), 98–104. https://doi.org/10.18201/ijisae.2022.272
Ming-Yang Su,Kun-Lin Chiang, Prevention of Wormhole Attacks in Mobile Ad Hoc Networks by Intrusion Detection Nodes. Springer-Verlag Berlin Heidelberg 2010,WASA2010, LNCS 6221, pp.253-260, 2010.
Garg, D. K. . (2022). Understanding the Purpose of Object Detection, Models to Detect Objects, Application Use and Benefits. International Journal on Future Revolution in Computer Science &Amp; Communication Engineering, 8(2), 01–04. https://doi.org/10.17762/ijfrcsce.v8i2.2066
Guoquan Li, Zheng Yan et al, A Study and Simulation Research of Blackhole Attack on Mobile AdHoc Network,IEEE CNS 2018-1st International Workshop on System Security and Vulnerability (SSV), 978-1-5386-4586-4/18.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





