Recent Trust Management Models for Secure IoT Ecosystem
Keywords:
Iot, Security framework, Trust Management, Classification of ModelsAbstract
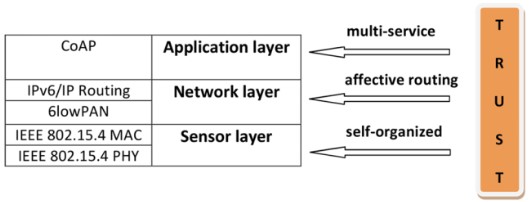
The emotional component of trust is crucial in the rapidly evolving world of computers. With a focus on distributed Trust Management systems, a variety of Trust Management frameworks and models have recently been developed for the Internet of Things (IoT). IoT systems may offer considerable advantages across a wide range of application sectors. These fields span everything from smart grid technology to home automation, environmental monitoring, and healthcare. However, there are numerous security concerns with the IoT, including challenges with trust management, key management, identification, and availability. The Internet of Things offers a realistic solution for threat management called "security by trust" (IoT). For symbiotic applications on the IoT stage, there is currently no clear-cut trust management framework. A framework's nodes' dependability should be evaluated in order to estimate the trust using the proper bounds. The parametrization of trust is not explicitly spelled out in existing models. Likewise, most existing models do not adequately depict trust erosion. Furthermore, trust recommendations are frequently given incorrect weights based on past trust, which increases the impact of poor recommendations. In this review paper, we'll cover about various trust models and how they affect Internet of Things security.
Downloads
References
Azad, M. A., Bag, S., Hao, F., & Shalaginov, A. (2020). Decentralized self-enforcing trust management system for social internet of things. Internet of Things Journal IEEE, 7(4), 2690-2703. https://doi.org/10.1109/JIOT.2019.2962282
Shafique, K.; Khawaja, B.A.; Sabir, F.; Qazi, S.; Mustaqim, M. Internet of Things (IoT) for Next-Generation Smart Systems: A Review of Current Challenges, Future Trends and Prospects for Emerging 5G-IoT Scenarios. IEEE Access 2020, 8, 23022–23040.
C. Sobin, “A survey on architecture, protocols and challenges in IoT,” Wireless Pers. Commun., vol. 112, pp. 1383–1429, Jan. 2020
Sharma, A., Pilli, E. S., Mazumdar, A. P., & Gera, P. (2020). Towards trustworthy Internet of Things: A survey on Trust Management applications and schemes. Computer Communications, 160, 475-493.
N. C. Luong, D. T. Hoang, P. Wang, D. Niyato, D. I. Kim, and Z. Han. Data collection and wireless communication in internet of things (IoT) using economic analysis and pricing models: A survey. IEEE Communications Surveys Tutorials, 18(4):2546– 2590, Fourth quarter 2019. ISSN 1553-877X. doi: 10.1109/COMST.2016.2582841
Hassija, V.; Chamola, V.; Saxena, V.; Jain, D.; Goyal, P.; Sikdar, B. A Survey on IoT Security: Application Areas, Security Threats, and Solution Architectures. IEEE Access 2019, 7, 82721–82743.
Ahmed, A.I.A.; Ab Hamid, S.H.; Gani, A.; Khan, S.; Khan, M.K. Trust and reputation for Internet of Things: Fundamentals, taxonomy, and open research challenges. J. Netw. Comput. Appl. 2019, 145, 102409
Jayasinghe, U.; Lee, G.M.; Um, T.-W.; Shi, Q. Machine Learning Based Trust Computational Model for IoT Services. IEEE Trans. Sustain. Comput. 2019, 4, 39–52.
Chen, I. R., Guo, J., & Bao, F. (2019). Trust management for SOA-based IoT and its application to service composition. IEEE Transactions on Services Computing, 9(3), 482-495. https://doi.org/10.1109/TSC.2014.2365797
Kim, B.-S., Hassan, S., & Khan, M. K. (2018). Trust management techniques for the Social Internet of Things: A survey. IEEE Access, 7, 29763-29787. https://doi.org/10.1109/ACCESS.2018.2880838
M. Frustaci, P. Pace, G. Aloi, and G. Fortino. Evaluating critical security issues of the IoT world: Present and future challenges. IEEE Internet of Things Journal, 5(4):2483–2495, Aug 2018. ISSN 2327-4662. Doi: 10.1109/JIOT.2017.2767291.
Djedjig, N.; Tandjaoui, D.; Romdhani, I.; Medjek, F. Trust management in the internet of things. In Security and Privacy in Smart Sensor Networks; IGI Global: Hershey, PA, USA, 2018; pp. 122–146.
V. Gazis. A survey of standards for machine-to-machine and the internet of things. IEEE Communications Surveys Tutorials, 19(1):482–511, first quarter 2017. ISSN 1553-877X. Doi: 10.1109/COMST.2016.2592948.
U. Raza, P. Kulkarni, and M. Sooriyabandara. Low power wide area networks: An overview. IEEE Communications Surveys Tutorials, 19(2):855–873, second quarter 2017. ISSN 1553-877X. Doi: 10.1109/COMST.990 2017.2652320.
Pourghebleh, B.; Navimipour, N.J. Data aggregation mechanisms in the Internet of things: A systematic review of the literature and recommendations for future research. J. Netw. Comput. Appl. 2017, 97, 23–34
A. Arabsorkhi, M. Sayad Haghighi, and R. Ghorbanloo. A conceptual trust model for the internet of things interactions. In 2016 8th International Symposium on Telecommunications (IST), pages 89–93, Sept 2016.doi: 10.1109/ISTEL.2016.7881789.
Goar, . V. K. ., and N. S. . Yadav. “Business Decision Making by Big Data Analytics”. International Journal on Recent and Innovation Trends in Computing and Communication, vol. 10, no. 5, May 2022, pp. 22-35, doi:10.17762/ijritcc.v10i5.5550.
Roman, R., P. Najera, and J. Lopez. (2011) “Securing the Internet of Things,” Computer (Long. Beach. Calif) 44 (9): 51–58.
https://www.statista.com/statistics/1101442/iot-number-of- connected-devices- worldwide/#:~:text=The%20total%20installed%20base%20o f,that%20are%20expected%20in%202021.
Chen, I. R., J. Guo, and F. Bao. (2016) “Trust Management for SOA-Based IoT and Its Application to Service Composition.” IEEE Trans. Serv. Comput. 9 (3): 482–495.
Albishi, S., B. Soh, A. Ullah, and F. Algarni. (2017) “Challenges and Solutions for Applications and Technologies in the Internet of Things.” Procedia Comput. Sci. 124: 608– 614.
Yan, Z., P. Zhang, and A. V. Vasilakos. (2014) “A Survey on Trust Management for Internet of Things.” J. Netw. Comput. Appl. 42: 120– 134.
Jiang, J., G. Han, F. Wang, L. Shu, and M. Guizani (2015) “An Efficient Distributed Trust Model for Wireless Sensor Networks.” IEEE Trans. Parallel Distrib. Syst. 26 (5): 1228– 1237.
Sicari, S., A. Rizzardi, L. A. Grieco, and A. Coen-Porisini. (2015) “Security, Privacy and Trust in Internet of Things: The Road Ahead.”
Guo, J., I. R. Chen, and J. J. P. Tsai. (2017) “A Survey of Trust Computation Models for Service Management in Internet of Things Systems.” Comput. Commun. 97: 1–14.
Ammar, M., G. Russello, and B. Crispo. (2018) “Internet of Things: A survey on the security of IoT frameworks.” J. Information Security Appl. 38: 8–27.
N. Marchang and R. Datta, “Light-weight trust-based routing protocol for mobile ad hoc networks,” IET Information security, vol. 6, no. 2, pp. 77–83, 2012.
A. Tajeddine, A. Kayssi, A. Chehab, I. Elhajj, and W. Itani, “Centera: a centralized trust-based efficient routing protocol with authentication for wireless sensor networks,” Sensors, vol. 15, no. 2, pp. 3299–3333, 2015.
N. Truong, H. Lee, B. Askwith and G. Lee, "Toward a Trust Evaluation Mechanism in the Social Internet of Things," SENSORS, vol. 17, no. 6, 2017
M. Ge and M. Helfert, "Data and information quality assessment in information manufacturing system," in International Conference on Business Information Systems, 2008.
N. Askham, D. Cook, M. Doyle, H. Fereday, M. Gibson, U. Landbeck, R. .. Lee, C. Maynard, G. Palmer and J. Schwarzenbach, "The six primary dimensions for data quality assessment," DAMA UK Working Group, United Kingdom, 2013.
N. Laranjeiro, S. Soydemir and J. Bernardino, "A survey on data quality: classifying poor data," in IEEE 21st Pacific Rim International Symposium on Dependable Computing (PRDC), 2015
Gupta, D. J. . (2022). A Study on Various Cloud Computing Technologies, Implementation Process, Categories and Application Use in Organisation. International Journal on Future Revolution in Computer Science &Amp; Communication Engineering, 8(1), 09–12. https://doi.org/10.17762/ijfrcsce.v8i1.2064
N. B. Truong, T. Um, B. Zhou and G. M. Lee, "Frompersonal experience to global reputation for trust evaluation in the social internet of things," in IEEE Global Communications Conference (GLOBECOM), Singapore, 2017.
Chen, I. R., J. Guo, and F. Bao. (2016) “Trust Management for SOA-Based IoT and Its Application to Service Composition.” IEEE Trans. Serv. Comput. 9 (3): 482–495.
Albishi, S., B. Soh, A. Ullah, and F. Algarni. (2017) “Challenges and Solutions for Applications and Technologies in the Internet of Things.” Procedia Comput. Sci. 124: 608– 614.
Kabisha, M. S., Rahim, K. A., Khaliluzzaman, M., & Khan, S. I. (2022). Face and Hand Gesture Recognition Based Person Identification System using Convolutional Neural Network. International Journal of Intelligent Systems and Applications in Engineering, 10(1), 105–115. https://doi.org/10.18201/ijisae.2022.273
Mendoza, C. V., & Kleinschmidt, J. H. (2015). Mitigating on-off attacks in the internet of things using a distributed trust management scheme. International Journal of Distributed Sensor Networks, 11(11), 859731.
Saied, Y. B., Olivereau, A., Zeghlache, D., & Laurent, M. (2013). Trust management system design for the Internet of Things: A context-aware and multi-service approach. Computers & Security, 39, 351-365.
Wosowei, J., & Shastry, C. Novel Research on Challenges and Directions for Trust Management in Social Internet of Things (SIOT).
Han, G., Jiang, J., Shu, L., Niu, J., & Chao, H. C. (2014). Management and applications of trust in Wireless Sensor Networks: A survey. Journal of Computer and System Sciences, 80(3), 602-617.
N. A. Libre. (2021). A Discussion Platform for Enhancing Students Interaction in the Online Education. Journal of Online Engineering Education, 12(2), 07–12. Retrieved from http://onlineengineeringeducation.com/index.php/joee/article/view/49
Shaikh, R. A., Jameel, H., d'Auriol, B. J., Lee, H., Lee, S., & Song, Y. J. (2009). Group-based trust management scheme for clustered wireless sensor networks.IEEE transactions on parallel and distributed systems, 20(11), 1698-1712
Bao, F., Chen, R., Chang, M., & Cho, J. H. (2012). Hierarchical trust management for wireless sensor networks and its applications to trust-based routing and intrusion detection.IEEE transactions on network and service management, 9(2), 169-183.
Al-Fuqaha, A., Guizani, M., Mohammadi, M., Aledhari, M., & Ayyash, M. (2015). Internet of things: A survey on enabling technologies, protocols, and applications. IEEE Communications Surveys & Tutorials, 17(4), 2347-2376.
Yan, Z., Zhang, P., &Vasilakos, A. V. (2014). A survey on trust management for Internet of Things.Journal of network and computer applications, 42, 120-134.
Sicari, S., Rizzardi, A., Grieco, L. A., &Coen-Porisini, A. (2015). Security, privacy and trust in Internet of Things: The road ahead. Computer Networks, 76, 146-164.
Ali, B.; Awad, A.I. Cyber and Physical Security Vulnerability Assessment for IoT-Based Smart Homes. Sensors 2018, 18, 817
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





