A Study on the Sound Recognition Method of Autonomous Vehicle using CNN
Keywords:
Autonomous Vehicle, Audio Recognition, Deep Learning, Convolutional Neural Network, Mel-spectrogramAbstract
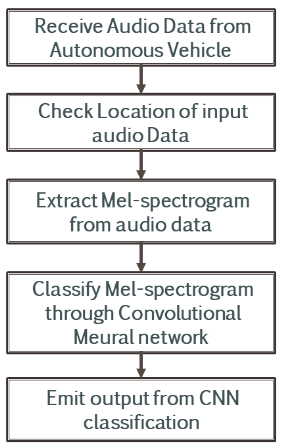
In this paper, a study on the algorithm that recognizes and judges sound source using convolutional neural network (CNN) is introduced. It is assumed that multiple of microphones are attached to receive sound information. The received sound information is then converted to visual information with the Mel-spectrogram which expands 1-dimensional sound information to 2-dimensional information. However, the shorter the extraction time by reducing n_mels, the lower the resolution of the image and the lower the performance as learning data. The value of n_mels = 64 is suggested to minimize the extraction time of Mel-spectrogram because this algorithm should be used in the autonomous vehicle. Through the computational experiment, 95% accuracy was obtained through CNN, machine learning.
Downloads
References
Y. U. Kim, “A Study on Multiple Sound Source Recognition Algorithm to Improve the Abient Detection Ability of Autonomous Vehicle”, 2019
Sarma, C. A. ., S. . Inthiyaz, B. T. P. . Madhav, and P. S. . Lakshmi. “An Inter Digital- Poison Ivy Leaf Shaped Filtenna With Multiple Defects in Ground for S-Band Bandwidth Applications”. International Journal on Recent and Innovation Trends in Computing and Communication, vol. 10, no. 8, Aug. 2022, pp. 55-66, doi:10.17762/ijritcc.v10i8.5668.
Towards Data Science. http://towardsdatascience.com
O'REILLY, “Hands on Machine Learning with scikit learn & tensorflow”, Oreilly & AssociatesInc, 2017.
Kumar, S., Gornale, S. S., Siddalingappa, R., & Mane, A. (2022). Gender Classification Based on Online Signature Features using Machine Learning Techniques. International Journal of Intelligent Systems and Applications in Engineering, 10(2), 260–268. Retrieved from https://ijisae.org/index.php/IJISAE/article/view/2020
K. H. YU, “Deep-Learning based scream recognition and implementation of scream alarm system”, 2018.
Silveira, M. R. ., Cansian, A. M. ., Kobayashi, H. K. ., & da Silva, L. M. (2022). Early Identification of Abused Domains in TLD through Passive DNS Applying Machine Learning Techniques. International Journal of Communication Networks and Information Security (IJCNIS), 14(1). https://doi.org/10.17762/ijcnis.v14i1.5256
Jalaj Thanaki, “Python Natural Language Processing: Advanced machine learning and deep learning techniques for natural language processing”, Packt Publishing, 2017.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





