Multilevel Approach for Cryptography using Genetic Algorithms with Existing S-DES Key Generation Method
Keywords:
Cipher, Cryptography, Genetic Algorithm, Key Size, SDESAbstract
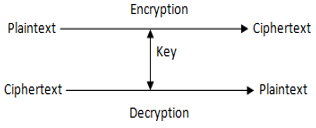
Cryptography is the art of writing secret codes. Cryptographers try to write secret codes. Cryptanalysts will break secret codes. Cryptographers and cryptanalysts always try to be ahead of each other. Genetic algorithms (GA) are structured yet randomized search algorithm invented by Darwinian’s evolutionary ideas about natural selection and genetics. The field of security is colossal and vast. Many researchers are working in this field to achieve security and privacy. Researchers tried different evolutionary algorithms for cryptography. This paper discussed the multilevel approach for Cryptography using the S-DES Key Generation method and genetic algorithm. Convergence of S-DES and Genetic Algorithm is more secure and unbreakable than traditional cryptosystem.
Downloads
References
D. E. Goldberg, “Genetic Algorithms in Search, Optimization, and Machine Learning”, 4th ed, Pearson Education, 2009.
A. R. Dalimunthe, H. Mawengkang, S. Suwilo, and A. Nazam, “Vernam Cipher with Complement Method and Optimization Key with Genetic Algorithm,” Journal of Physics: Conference Series, 2019.
S. K. Pujari, G. Bhattacharjee, and S. A. Bhoi, “Hybridized Model for Im- age Encryption through Genetic Algorithm and DNA Sequence,” Procedia Computer Science, 2018.
A. Sen, A. Ghosh, and A. Nath, “Bit level symmetric key cryptography using genetic algorithm,” Proceedings - 7th International Conference on Communication Systems and Network Technologies, 2017.
S. F. U. Khan and Bhatia, “A NOVEL APPROACH TO GENETIC ALGO- RITHM BASED CRYPTOGRAPHY,” International Journal of Research in Computer Science, vol. 2, no. 3, pp. 7–10, 2012.
W. Stallings, “Cryptography and Network security Principles and Practices”, Pearson Education, Fourth Edition, 2010.
B. Delman, “Genetic Algorithms in Cryptography”, Ronchester Institute of Technology, New York, 2004.
R. Toemeh and S. Arumugam, “Applying Genetic Algorithms for Searching Key-Space of Polyalphabetic Substitution Ciphers,” The International Arab Journal of Information Technology, vol. 5, no. 1, 2008.
Dr, G. Poornima, G. R. Naik, and Naik, “Asymmetric Key Encryption using Genetic Algorithm,” International Journal of Latest Trends in Engineering and Technology (IJLTET), vol. 3, no. 3, 2014.
D. Dr, P. Singh, D. R. Rani, and Kumar, “To Design a Genetic Algorithm for Cryptography to Enhance the Security,” International Journal of Innovations in Engineering and Technology (IJIET), vol. 2, 2013.
P. Garg, “A Comparison between Memetic algorithm and Genetic al-gorithm for the cryptanalysis of Simplified Data Encryption Standard algorithm,” International Journal of Network Security & Its Applications (IJNSA), vol. 1, no. 1, 2013.
L. Sharma and B. K. P. Ramgopal Sharma, “Breaking of Simplified Data Encryption Standard Using Genetic Algorithm,” Global Journal of Computer Science and Technology, vol. 12, no. 5, 2012.
G. Patel, “Genetic Algorithm for Cryptanalysis”, BITs Pilani,2008.
K. Sindhuja and D. S. Pramela, “Symmetric Key Encryption Technique Using Genetic Algorithm,” International Journal of Computer Science and Information Technologies (IJCSIT), vol. 5, no. 1, pp. 414–416, 2014.
D. R. M. L. Vimalathithan and Valarmathi, “Cryptanalysis of S-DES using Genetic Algorithm,” International Journal of Recent Trends in Engineering, vol. 2, no. 4, 2009.
A. Kumar and M. K. Ghose, “Information Security using Genetic Algorithm and Chaos”, 2007.
A. K. Verma, M. Dave, and R. C. Joshi, “Genetic Algorithm and Tabu Search Attack on the Mono-Alphabetic Substitution Cipher in Adhoc Networks,” Journal of Computer Science, vol. 3, no. 3, pp. 134–137, 2007.
G. N. Rajendra and B. R. Kaur, “A New Approach for Data Encryption Using Genetic Algorithms and Brain Mu Waves,” International Journal of Scientific and Engineering Research, vol. 2, 2011.
P. A. Bagane and K. V. Kulhalli, “Genetic Algorithm for Cryptography,” International Journal of Computer Application, vol. 1, 2015.
P. A. Bagane and S. Kotrappa, “Cryptanalysis for S-DES using Genetic Algorithm,” International Journal of Technology and Science, no. 2, 2016.
P. Bagane and S. Kotrappa, “Bibliometric Survey for Cryptanalysis of Block Ciphers towards Cyber Security”, Library Philosophy and Practice, 2020.
P. Bagane and S. Kotrappa, “Comparison between traditional cryptographic methods and ge- netic algorithm based method towards Cyber Security,” International Journal of Advanced Research in Engineering and Technology (IJARET), vol. 12, no. 2, pp. 676–682, 2021.
K. Sandyarani and P. N. Kumar, “Design and analysis of AES-CM with non-linearity S-box architecture,” International Conference on Current Trends in Engineering and Technology (ICCTET), pp. 252–254, 2013.
F. Rao and J. Tan, “Energy consumption research of AES encryption al- gorithm in ZigBee,” International Conference on Cyberspace Technology, pp. 1–6, 2014.
S. Koteshwara, A. Das, and K. K. Parhi, “Performance comparison of AES-GCM-SIV and AES-GCM algorithms for authenticated encryption on FPGA platforms”, 51st Asilomar Conference on Signals, Systems, and Computers, pp. 1331-1336, 2017.
P. Bagane and D. K. Sirbi, “Enriching AES through the key generation from Genetic Algorithm,” Indian Journal of Computer Science and Engineering, vol. 12, no. 4, 2021.
R. S. Semente, A. O. Salazar, and F. D. M. Oliveira, “CRYSEED: An automatic 8-bit cryptographic algorithm developed with genetic programming,” IEEE International Instrumentation and Measurement Technology Conference (I2MTC) Proceedings, pp. 1065–1068, 2014.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





