Efficient Trust Inference Model for Pervasive Computing Based on Hybrid Deep Learning
Keywords:
Anomaly Detection, Machine Learning, Security, Pervasive Computing, Enhanced Trust modelAbstract
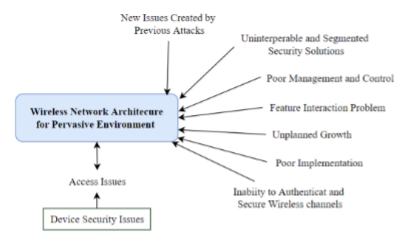
With the rise of mobile technology, pervasive computing has become an indispensable tool for processing and exchanging data in today’s connected society. For distributed computing services to be used in the same places where people live and socialise, pervasive computing must be present. Recent developments in pervasive computing have shifted the focus from stationary computers to mobile ones, such as laptops, notepads, cell phones, and PDAs. Devices in the pervasive environment are available on a global scale and are capable of receiving a wide range of audio-visual as well as other telecommunications services. Problems of user trust, data protection, and client and device node identification may arise for the system and users in this extensive setting. In this study, we proposed an efficient trust inference model for ubiquitous computing associated fine-tuned ANN and ML IoT attack predictor which reached an accuracy of 90.43%.
Downloads
References
Z. Allam and Z. A. Dhunny, “On big data, artificial intelligence and smart cities,” Cities, vol. 89, pp. 80-91, 2019
W. Shi, J. Cao, Q. Zhang, Y. Li, and L. Xu, “Edge computing: Vision and challenges,’ IEEE internet of things journal, vol. 3, no. 5, pp. 637-646, 2016.
C. Becker, C. Julien, P. Lalanda, and F. Zambonelli, “Pervasive computing middleware: current trends and emerging challenges,” CCF Transactions on Pervasive Computing Interaction, vol. 1, no. 1, pp. 10-23, 2019.
J. Amarnath, P. G. Shah, and H. Chandramouli, “Advanced Key Management System (AKMS) for Security in Public Clouds,” in Evolution in Computational Intelligence: Springer, pp. 573-582, 2021.
F. J. I. P. C. Alt, “Pervasive Security and Privacy—A Brief Reflection on Challenges and Opportunities,” vol. 20, no. 4, pp. 82-86, 2021.
S. Kaushik and C. Gandhi, “Security and Privacy Issues in Fog/Edge/Pervasive Computing,” Fog, Edge, Pervasive Computing in Intelligent IoT Driven Applications, pp. 369-387, 2020.
A. Gouarir, G. Martínez-Arellano, G. Terrazas, P. Benardos, and S. Ratchev, “In-process tool wear prediction system based on machine learning techniques and force analysis,” Procedia CIRP, vol. 77, pp. 501-504, 2018.
D. Mukhametov, “Ubiquitous computing and distributed machine learning in smart cities, in 2020 Wave Electronics and its Application in Information and Telecommunication Systems (WECONF), pp. 1-5, 2020. IEEE.
X.-G. Zhang, G.-H. Yang, and S. Wasly, “Man-in-the-middle attack against cyber-physical systems under random access protocol,” Information Sciences, vol. 576, pp. 708-724, 2021.
V. Punitha, C. Mala, and N. Rajagopalan, “A novel deep learning model for detection of denial of service attacks in HTTP traffic over internet,” International Journal of Ad Hoc Ubiquitous Computing, vol. 33, no. 4, pp. 240-256, 2020.
Y. Liang, Y. Qin, Q. Li, X. Yan, L. Huangfu, S. Samtani, B. Guo, Z. Yu. “An Escalated Eavesdropping Attack on Mobile Devices via Low-Resolution Vibration Signals,” IEEE Transactions on Dependable Secure Computing, 2022.
M. Salimitari, M. Chatterjee, and Y. P. J. I. o. T. Fallah,. “A survey on consensus methods in blockchain for resource-constrained IoT networks,” Internet of Things, vol. 11, p. 100212, 2020.
A. Waheed, A.I/ Umar, M. Zareei, N. Din, N.U. Amin, J. Iqbal, Y. Saeed, E.M. Mohamed, “Cryptanalysis and improvement of a proxy signcryption scheme in the standard computational model,” IEEE Access, vol. 8, pp. 131188-131201, 2020.
A. Mahfouz, A. Abuhussein, D. Venugopal, and S. Shiva, “Ensemble classifiers for network intrusion detection using a novel network attack dataset,” Future Internet, vol. 12, no. 11, p. 180, 2020.
X. Yao, F. Farha, R. Li, I. Psychoula, L. Chen, and H. Ning, “Security and privacy issues of physical objects in the IoT: Challenges and opportunities,” Digital Communications Networks, vol. 7, no. 3, pp. 373-384, 2021.
D. Y. Huang, N. Apthorpe, F. Li, G. Acar, and N. Feamster, “Iot inspector: Crowd sourcing labeled network traffic from smart home devices at scale,” Proceedings of the ACM on Interactive, Mobile, Wearable Ubiquitous Technologies, vol. 4, no. 2, pp. 1-21, 2020.
J. Shahid, R. Ahmad, A. K. Kiani, T. Ahmad, S. Saeed, and A. M. Almuhaideb, “Data protection and privacy of the internet of healthcare things (IoHTs),” Applied Sciences, vol. 12, no. 4, p. 1927, 2022.
M. Langheinrich and F. Schaub, “Privacy in mobile and pervasive computing,” Synthesis Lectures on Mobile Pervasive Computing, vol. 10, no. 1, pp. 1-139, 2018.
H. A. Abdulghani, N. A. Nijdam, A. Collen, and D. Konstantas, “A study on security and privacy guidelines, countermeasures, threats: IoT data at rest perspective,” Symmetry, vol. 11, no. 6, p. 774, 2019.
G. Chen, M. Li, and D. Kotz, “Data-centric middleware for context-aware pervasive computing,” Pervasive mobile computing, vol. 4, no. 2, pp. 216-253, 2008.
E. Katsiri and A. Mycroft, “Linking temporal first-order logic with Bayesian networks for the simulation of pervasive computing systems,” Simulation Modelling Practice Theory, vol. 19, no. 1, pp. 161-180, 2011.
A. Padovitz, S. W. Loke, and A. Zaslavsky, “The ECORA framework: A hybrid architecture for context-oriented pervasive computing,” Pervasive mobile computing, vol. 4, no. 2, pp. 182-215, 2008.
S. I. Ahamed, H. Li, N. Talukder, M. Monjur, and C. S. Hasan, “Design and implementation of S-MARKS: A secure middleware for pervasive computing applications,” Journal of Systems Software, vol. 82, no. 10, pp. 1657-1677, 2009.
A. Boukerche and Y. Ren, “A trust-based security system for ubiquitous and pervasive computing environments,” Computer communications, vol. 31, no. 18, pp. 4343-4351, 2008.
P. Yu, X. Ma, J. Cao, J. J. P. Lu, and M. “Computing, Application mobility in pervasive computing: A survey,” vol. 9, no. 1, pp. 2-17, 2013.
A. B. Usman and J. Gutierrez, “Toward trust based protocols in a pervasive and mobile computing environment: A survey,” Ad Hoc Networks, vol. 81, pp. 143-159, 2018.
G. Carullo, A. Castiglione, G. Cattaneo, A. De Santis, U. Fiore, and F. Palmieri, “Feeltrust: providing trustworthy communications in ubiquitous mobile environment,” in 2013 IEEE 27th International Conference on Advanced Information Networking and Applications (AINA), pp. 1113-1120, 2013. IEEE.
M. K. Denko, T. Sun, and I. Woungang, “Trust management in ubiquitous computing: A Bayesian approach,” Computer Communications, vol. 34, no. 3, pp. 398-406, 2011.
M. Ivanova, “Researching affective computing techniques for intelligent tutoring systems,” in 2013 International Conference on Interactive Collaborative Learning (ICL), pp. 596-602, 2013. IEEE.
Y. Chang, W. Li, and Z. Yang, “Network intrusion detection based on random forest and support vector machine,” in 2017 IEEE international conference on computational science and engineering (CSE) and IEEE international conference on embedded and ubiquitous computing (EUC), vol. 1, pp. 635-638, 2017.
U. Tariq, T. A. Ahanger, M. Nusir, and A. Ibrahim, “A Pervasive Computational Intelligence based Cognitive Security Co-design Framework for Hype-connected Embedded Industrial IoT,” International Journal of Computers, Communications Control, vol. 16, no. 2, 2021.
I. Ullah and Q. H. Mahmoud,.A scheme for generating a dataset for anomalous activity detection in iot networks, in Canadian Conference on Artificial Intelligence, pp. 508-520, 2020.
K. S. Athrey, Tutorial on Keras, ed: Cap, 2018.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





