Round S-Boxes Development for Present-80 Lightweight Block Cipher Encryption Algorithm
Keywords:
lightweight, algorithm, proposed, enhanced, encryption, present-80, S-boxes, P-layerAbstract
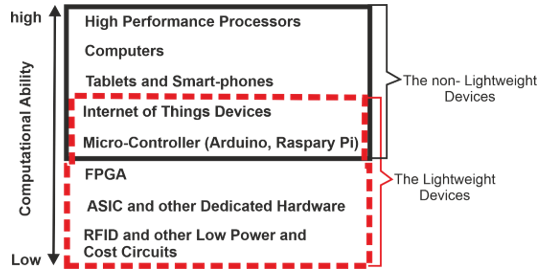
lightweight cryptography is a branch of encryption. It is symmetric encryption that is made to work on a variety of hardware that has low processing power, low cost, limited memory, and limited processing time. With a lightweight design, consideration is given to how to maintain a balance between usability and functionality while still maintaining an appropriate level of security. The present block cipher algorithm is one of them; it has a symmetric key and two versions—one with an 80-bit key and the other with a 128-bit key—each of which employed blocks of a 64-bit length. Present-80 algorithm, which is commonly used in IOT applications and has an 80-bit key length. In this study, an enhancement to the Present-80 encryption algorithm was proposed. The proposal involves the usage of sixteen separate S-boxes, eight of which are used for processing each round and eight for updating the roundkey. One of these eight boxes is used for each round to update the roundkey, which is determined by choosing three positions from the key for each round before it is updated and makes up an address between 0 and 7. Three different positions are selected in the same way that the active s-box for that round is chosen. The active s-box for each round of encryption/decryption processing is selected by the three-position key for that round before it is updated. At the end of the study, the throughput of the size and execution time of the original and modified algorithms were compared using a variety of data formats, including text, audio, image, and video, with varied sizes. The 16 NIST statistical randomness packages were used to test the randomness of the ciphertext sequences produced by the enhanced algorithm, and all of these tests were passed successful.
Downloads
References
M. Gutfleisch, J. H. Klemmer, N. Busch, Y. Acar, M. A. Sasse, and S. Fahl, “How does usable security (not) end up in software products? results from a qualitative interview study,” in 2022 IEEE Symposium on Security and Privacy (SP), 2022, pp. 893–910.
M. L. Villani et al., “A Modular Architecture of Command-and-Control Software in Multi-Sensor Systems Devoted to Public Security,” Information, vol. 14, no. 3, p. 162, 2023.
G. Bella, J. Ophoff, K. Renaud, D. Sempreboni, and L. Viganò, “Perceptions of beauty in security ceremonies,” Philos. Technol., vol. 35, no. 3, p. 72, 2022.
S. Gupta, M. Kumar, G. Singh, and A. Chanda, “Development of a Novel Footwear Based Power Harvesting System,” e-Prime-Advances Electr. Eng. Electron. Energy, p. 100115, 2023.
H. Chen et al., “BMS: Bandwidth-aware Multi-interface Scheduling for energy-efficient and delay-constrained gateway-to-device communications in IoT,” Comput. Networks, p. 109645, 2023.
M. Abujoodeh, L. Tamimi, and R. Tahboub, “Toward Lightweight Cryptography: A Survey,” in Computational Semantics, IntechOpen, 2023.
J. Kuang, Y. Guo, and L. Li, “IIoTBC: A Lightweight Block Cipher for Industrial IoT Security.,” KSII Trans. Internet Inf. Syst., vol. 17, no. 1, 2023.
F. Thabit, S. Alhomdy, A. H. A. Al-Ahdal, and S. Jagtap, “A new lightweight cryptographic algorithm for enhancing data security in cloud computing,” Glob. Transitions Proc., vol. 2, no. 1, pp. 91–99, 2021.
S. S. Dhanda, B. Singh, and P. Jindal, “Lightweight cryptography: a solution to secure IoT,” Wirel. Pers. Commun., vol. 112, pp. 1947–1980, 2020.
G. Bansod, N. Pisharoty, and A. Patil, “BORON: an ultra-lightweight and low power encryption design for pervasive computing,” Front. Inf. Technol. Electron. Eng., vol. 18, pp. 317–331, 2017.
S. Ashaq, M. Nazish, M. Ali, I. Sultan, and M. T. Banday, “FPGA Implementation of PRESENT Block Cypher with Optimised Substitution Box,” in 2022 Smart Technologies, Communication and Robotics (STCR), 2022, pp. 1–6.
N. Im, S. Choi, and H. Yoo, “S-Box Attack Using FPGA Reverse Engineering for Lightweight Cryptography,” IEEE Internet Things J., vol. 9, no. 24, pp. 25165–25180, 2022.
S. R. Ferianto and A. D. Handayani, “Strict Avalanche Criterion (SAC) Test on Lightweight Blockcipher Algorithms”.
C. Tezcan, “Key lengths revisited: GPU-based brute force cryptanalysis of DES, 3DES, and PRESENT,” J. Syst. Archit., vol. 124, p. 102402, 2022.
K. Jang, G. Song, H. Kim, H. Kwon, H. Kim, and H. Seo, “Efficient implementation of PRESENT and GIFT on quantum computers,” Appl. Sci., vol. 11, no. 11, p. 4776, 2021.
J. Guo, T. Peyrin, A. Poschmann, and M. Robshaw, “The LED block cipher,” in Cryptographic Hardware and Embedded Systems–CHES 2011: 13th International Workshop, Nara, Japan, September 28–October 1, 2011. Proceedings 13, 2011, pp. 326–341.
B. Chaitra, V. G. K. Kumar, and R. C. Shatharama, “A survey on various lightweight cryptographic algorithms on FPGA,” IOSR J. Electron. Commun. Eng., vol. 12, no. 1, pp. 45–59, 2017.
M. F. Mushtaq, S. Jamel, A. H. Disina, Z. A. Pindar, N. S. A. Shakir, and M. M. Deris, “A survey on the cryptographic encryption algorithms,” Int. J. Adv. Comput. Sci. Appl., vol. 8, no. 11, pp. 333–344, 2017.
A. Ramesh and A. Suruliandi, “Performance analysis of encryption algorithms for Information Security,” in 2013 International Conference on Circuits, Power and Computing Technologies (ICCPCT), 2013, pp. 840–844.
C. Liu, Y. Zhang, J. Xu, J. Zhao, and S. Xiang, “Ensuring the security and performance of IoT communication by improving encryption and decryption with the lightweight cipher uBlock,” IEEE Syst. J., vol. 16, no. 4, pp. 5489–5500, 2022.
L. Jin, M. Yi, Y. Xiao, L. Sun, Y. Lu, and H. Liang, “A dynamically reconfigurable entropy source circuit for high-throughput true random number generator,” Microelectronics J., p. 105690, 2023.
J. Rajski, M. Trawka, J. Tyszer, and B. Wlodarczak, “A Lightweight True Random Number Generator for Root of Trust Applications,” IEEE Trans. Comput. Des. Integr. Circuits Syst., 2023.
A. Slavković and J. Seeman, “Statistical data privacy: A song of privacy and utility,” Annu. Rev. Stat. Its Appl., vol. 10, 2023.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Ahmed Abdullah Khalil, Maytham Mustafa Hammood, Awni M. Gaftan

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





