Diffie-Hellman Key Exchange Based on Block Matrices Combined with Elliptic Curves
Keywords:
Diffe-Hellman Key Exchange, Elliptic Curves, ECDLPAbstract
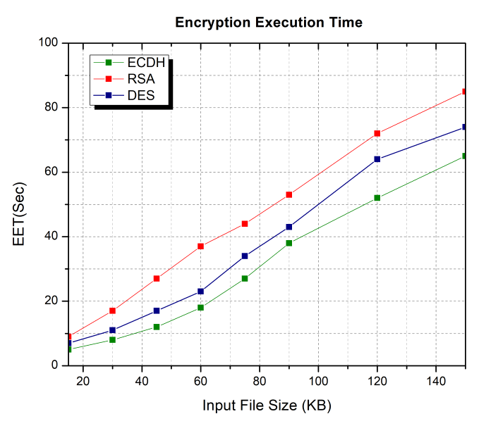
Various techniques were used to improve and propose cryptographic systems based on elliptic curves. In particular, the Diffie-Hellman key exchange protocol is widely used in most of these systems. In this work, we introduce an efficient approach based on the block matrices integrated with elliptic curves to increase the security of this protocol. With the new system, we can reduce key size without expanding the underlying elliptic curve. Therefore, the proposed protocol security will be more intractable since it will need to solve the Elliptic Curve Discrete Logarithm Problem more than once based on the chosen block matrices compared with the original protocol.
Downloads
References
N. Ferguson, B. Schneier and T. Konho. “Cryptography Engineering: Design Principles and Practical Applications”, John Wiley & Sons, 2011.
W. Stallings. “Cryptography and Network Security: Principles and Practice”, 7th ed.; Prentice Hall, Upper Saddle River, New Jersey, USA, 2017.
W. Diffie and M. E. Hellman. “New directions in cryptography”, IEEE Transactions on Information Theory, Vol. 22, No. 6, pp. 644-654, 1976.
D. Wong, “Real-world cryptography”, Simon and Schuster, 2021.
N. Koblitz. “Elliptic Curve Cryptosystems”. Mathematics of Computation, Vol. 48, No. 77, pp. 203-209, 1987.
V. Miller. “Uses of Elliptic Curves in cryptography”, In Advances in Cryptology-CRYPTO 85; Springer: Berlin/Heidelberg, Germany, pp. 417-426, 1986.
D. Johnson, A. Menezes, “The elliptic curve digital signature algorithm (ECDSA)”, International journal of information security, Vol. 1, No. 1, pp. 36-63, 2001.
Y.-J. Huang, C. Petit, N. Shinohara, and T. Takagi, “Improvement of FPPR method to solve ECDLP”, Pacific Journal of Mathematics for Industry, Vol. 7, No. 1, pp. 1-9, 2015.
J. J. Climent, F. Ferr´andez, J. F. Vicent, and A. Zamora. “A nonlinear elliptic curve cryptosystem based on matrices”, Applied Mathematics and Computation, Vol. 174, No. 1, pp. 150-164, 2006.
F. Amounas and E. H. El Kinani. “Fast mapping method based on matrix approach for elliptic curve cryptography”, International Journal of Information & Network Security (IJINS), Vol. 1, No. 2, pp. 54-59, 2012.
A. Chillali, C. Zakariae, and A. Mouhib. “Prof The" Elliptic" matrices and a new kind of cryptography”, Boletim da Sociedade Paranaense de Matemática Vol. 41, pp. 1-12, 2023.
A. A. Neamah, “New Collisions to Improve Pollard's Rho Method of Solving the Discrete Logarithm Problem on Elliptic Curves”, Journal of Computer Science, Vol. 11, No. 9, pp. 971-975, 2015.
Y. Jiang, Y. Shen, and Q. Zhu. “A lightweight key agreement protocol based on Chinese remainder theorem and ECDH for smart homes”, Sensors, Vol. 20, No. 5, pp. 1-13, 2020.
C. A. Lara-Nino, A. Diaz-Perez, and M. Morales-Sandoval, “Elliptic curve lightweight cryptography: A survey,” IEEE Access, Vol. 6, pp. 72514-72550, 2018.
R. A. Horn and C. R. Johnson, “Topics in Matrix Analysis”, Cambridge University Press, 1994.
Pentyala, S., Liu, M., & Dreyer, M. (2019). Multi-task networks with universe, group, and task feature learning. arXiv preprint arXiv:1907.01791.
Srivastava, Swapnita, and P. K. Singh. "Proof of Optimality based on Greedy Algorithm for Offline Cache Replacement Algorithm." International Journal of Next-Generation Computing 13.3 (2022).
Smiti, Puja, Swapnita Srivastava, and Nitin Rakesh. "Video and audio streaming issues in multimedia application." 2018 8th International Conference on Cloud Computing, Data Science & Engineering (Confluence). IEEE, 2018.
Srivastava, Swapnita, and P. K. Singh. "HCIP: Hybrid Short Long History Table-based Cache Instruction Prefetcher." International Journal of Next-Generation Computing 13.3 (2022).
Srivastava, Swapnita, and Shilpi Sharma. "Analysis of cyber related issues by implementing data mining Algorithm." 2019 9th International Conference on Cloud Computing, Data Science & Engineering (Confluence). IEEE, 2019.
P Mall and P. Singh, “Credence-Net: a semi-supervised deep learning approach for medical images,” Int. J. Nanotechnol., vol. 20, 2022.
Narayan, Vipul, et al. "Deep Learning Approaches for Human Gait Recognition: A Review." 2023 International Conference on Artificial Intelligence and Smart Communication (AISC). IEEE, 2023.
Narayan, Vipul, et al. "FuzzyNet: Medical Image Classification based on GLCM Texture Feature." 2023 International Conference on Artificial Intelligence and Smart Communication (AISC). IEEE, 2023.
"Keyboard invariant biometric authentication." 2018 4th International Conference on Computational Intelligence & Communication Technology (CICT). IEEE, 2018.
Mall, Pawan Kumar, et al. "Early Warning Signs Of Parkinson’s Disease Prediction Using Machine Learning Technique." Journal of Pharmaceutical Negative Results (2023): 2607-2615.
Choudhary, Shubham, et al. "Fuzzy approach-based stable energy-efficient AODV routing protocol in mobile ad hoc networks." Software Defined Networking for Ad Hoc Networks. Cham: Springer International Publishing, 2022. 125-139.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





