Intrusion Detection in the Digital Age: A Hybrid Data Optimization Perspective
Keywords:
Intrusion detection system, cyber-attack, threat, security, Machine learningAbstract
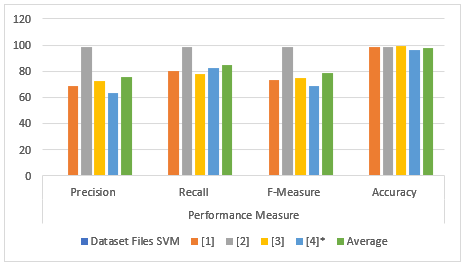
The ever-growing use of technology has resulted in a considerable rise in the total number of cyber threats and security breaches. Intrusion detection systems (IDSs) have become an crucial tool in combating these threats by detecting and preventing unauthorized access to computer systems and networks. In this research paper, we present a hybrid data optimization perspective on intrusion detection in the digital age. The importance of IDS cannot be overstated in the current digital landscape. With the increasing sophistication of cyber threats, traditional intrusion detection methods may prove insufficient. A hybrid approach that combines the strengths of multiple algorithms can lead to improved accuracy and reduced false alarms. In our research, we use a hybrid feature selection approach that combines genetic algorithms (GA) and random forest (RF) to choose the most important characteristics for the purpose of intrusion detection. The proposed hybrid approach to detecting intrusions has been shown to significantly improve the system's accuracy compared to the use of both RF and GA alone. We performed a comprehensive evaluation of the three algorithms, namely the SVM-RF, the support vector machine (SVM) and the random forest. Our research provides a valuable contribution to the field of intrusion detection by presenting a hybrid data optimization perspective that can significantly improve the accuracy of intrusion detection systems. This work can be used as a reference for future research in the area and can be applied in real-world intrusion detection systems to provide better protection against cyber threats.
Downloads
References
T. Rupa Devi and S. Badugu, A Review on Network Intrusion Detection System Using Machine Learning. Springer International Publishing, 2020.
A. Thakkar and R. Lohiya, A Review on Machine Learning and Deep Learning Perspectives of IDS for IoT: Recent Updates, Security Issues, and Challenges, vol. 28, no. 4. Springer Netherlands, 2021.
P. Parkar and A. Bilimoria, “A survey on cyber security IDS using ML methods,” Proc. - 5th Int. Conf. Intell. Comput. Control Syst. ICICCS 2021, no. ICICCS, pp. 352–360, 2021, doi: 10.1109/ICICCS51141.2021.9432210.
P. Shukla, “ML-IDS: A machine learning approach to detect wormhole attacks in Internet of Things,” 2017 Intell. Syst. Conf. IntelliSys 2017, vol. 2018-Janua, no. September, pp. 234–240, 2018, doi: 10.1109/IntelliSys.2017.8324298.
E. S. G.S.R., M. Azees, C. H. Rayala Vinodkumar, and G. Parthasarathy, “Hybrid optimization enabled deep learning technique for multi-level intrusion detection,” Adv. Eng. Softw., vol. 173, no. June, p. 103197, 2022, doi: 10.1016/j.advengsoft.2022.103197.
Sashank, Y. T. ., Kakulapati, V. ., & Bhutada, S. . (2023). Student Engagement Prediction in Online Session. International Journal on Recent and Innovation Trends in Computing and Communication, 11(2), 43–47. https://doi.org/10.17762/ijritcc.v11i2.6108
N. Kunhare, R. Tiwari, and J. Dhar, “Particle swarm optimization and feature selection for intrusion detection system,” Sadhana - Acad. Proc. Eng. Sci., vol. 45, no. 1, pp. 1–14, 2020, doi: 10.1007/s12046-020-1308-5.
A. Alzaqebah, I. Aljarah, O. Al-Kadi, and R. Damaševičius, “A Modified Grey Wolf Optimization Algorithm for an Intrusion Detection System,” Mathematics, vol. 10, no. 6, pp. 1–16, 2022, doi: 10.3390/math10060999.
S. K. Gupta, M. Tripathi, and J. Grover, “Hybrid optimization and deep learning based intrusion detection system,” Comput. Electr. Eng., vol. 100, no. February, p. 107876, 2022, doi: 10.1016/j.compeleceng.2022.107876.
A. Ponmalar and V. Dhanakoti, “An intrusion detection approach using ensemble Support Vector Machine based Chaos Game Optimization algorithm in big data platform,” Appl. Soft Comput., vol. 116, p. 108295, 2022, doi: 10.1016/j.asoc.2021.108295.
E. Balamurugan, A. Mehbodniya, E. Kariri, K. Yadav, A. Kumar, and M. Anul Haq, “Network optimization using defender system in cloud computing security based intrusion detection system withgame theory deep neural network (IDSGT-DNN),” Pattern Recognit. Lett., vol. 156, pp. 142–151, 2022, doi: 10.1016/j.patrec.2022.02.013.
M. H. Nasir, S. A. Khan, M. M. Khan, and M. Fatima, “Swarm Intelligence inspired Intrusion Detection Systems — A systematic literature review,” Comput. Networks, vol. 205, no. August 2021, p. 108708, 2022, doi: 10.1016/j.comnet.2021.108708.
Y. Y. Chung and N. Wahid, “A hybrid network intrusion detection system using simplified swarm optimization (SSO),” Appl. Soft Comput. J., vol. 12, no. 9, pp. 3014–3022, 2012, doi: 10.1016/j.asoc.2012.04.020.
P. R. K. Varma, V. V. Kumari, and S. S. Kumar, “Feature Selection Using Relative Fuzzy Entropy and Ant Colony Optimization Applied to Real-time Intrusion Detection System,” Procedia Comput. Sci., vol. 85, pp. 503–510, 2016, doi: 10.1016/j.procs.2016.05.203.
J. K. Samriya, R. Tiwari, X. Cheng, R. K. Singh, A. Shankar, and M. Kumar, “Network intrusion detection using ACO-DNN model with DVFS based energy optimization in cloud framework,” Sustain. Comput. Informatics Syst., vol. 35, no. September 2021, p. 100746, 2022, doi: 10.1016/j.suscom.2022.100746.
S. S. Roy, V. Madhu Viswanatham, P. Venkata Krishna, N. Saraf, A. Gupta, and R. Mishra, “Applicability of rough set technique for data investigation and optimization of intrusion detection system,” Lect. Notes Inst. Comput. Sci. Soc. Telecommun. Eng. LNICST, vol. 115, pp. 479–484, 2013, doi: 10.1007/978-3-642-37949-9_42.
Hiroshi Yamamoto, An Ensemble Learning Approach for Credit Risk Assessment in Banking , Machine Learning Applications Conference Proceedings, Vol 1 2021.
L. Yang and A. Shami, “A Transfer Learning and Optimized CNN Based Intrusion Detection System for Internet of Vehicles,” IEEE Int. Conf. Commun., vol. 2022-May, pp. 2774–2779, 2022, doi: 10.1109/ICC45855.2022.9838780.
S. Shitharth, P. R. Kshirsagar, P. K. Balachandran, K. H. Alyoubi, and A. O. Khadidos, “An Innovative Perceptual Pigeon Galvanized Optimization (PPGO) Based Likelihood Naïve Bayes (LNB) Classification Approach for Network Intrusion Detection System,” IEEE Access, vol. 10, pp. 46424–46441, 2022, doi: 10.1109/ACCESS.2022.3171660.
S. Shyla, V. Bhatnagar, V. Bali, and S. Bali, “Optimization of Intrusion Detection Systems Determined by Ameliorated HNADAM-SGD Algorithm,” Electron., vol. 11, no. 4, pp. 1–21, 2022, doi: 10.3390/electronics11040507.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





