An Intelligent Intrusion Detection and Classification System using CSGO-LSVM Model for Wireless Sensor Networks (WSNs)
Keywords:
Wireless Sensor Network (WSN), Cuckoo Search – Greedy Optimization (CSGO), Network Security, Preprocessing, Intrusion Detection System (IDS), Support Vector Machine (SVM) ClassificationAbstract
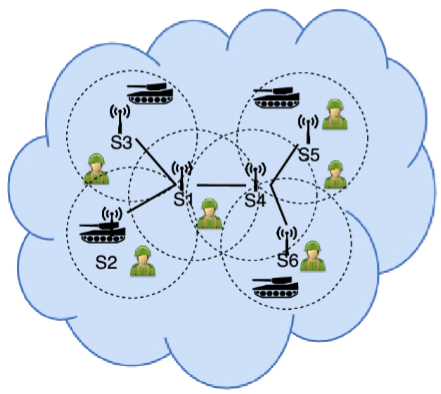
Providing security to the Wireless Sensor Networks (WSN) is more challenging process in recent days, due to the self-organization nature and randomness of sensor nodes. For this purpose, the Intrusion Detection System (IDS) is mainly developed that supports to increase the security of network against the harmful intrusions. The conventional IDS security frameworks are highly concentrating on improving the reliability and safety of networks by using different approaches. Still, it limits with key problems of increased time consumption, more delay, and reduced efficiency, inefficient handling of large dimensional datasets, and high misclassification outputs. In order to solve these problems, the proposed work develops an intelligent IDS framework for enhancing the security of WSN by using the Cuckoo Search Greedy Optimization (CSGO) and Likelihood Support Vector Machine (LSVM) models. In this model, the most extensively used network datasets such as NSL-KDD and UNSW-NB15 are considered for validating this model. Initially, the dataset preprocessing is performed for normalizing the attributes based on the processes of irrelevant information removal, missing value prediction, and filtering. After preprocessing, the optimal number of features are selected and given to the input of CSGO algorithm, which computes the optimal fitness function for selecting the best features. Finally, the LSVM based machine learning classification technique is utilized for predicting the classified label as whether normal or abnormal. During results evaluation, the performance of the proposed security model is validated and compared by using different performance measures.
Downloads
References
C. Ioannou, and V. Vassiliou, “Network Attack Classification in IoT Using Support Vector Machines,” Journal of Sensor and Actuator Networks, vol. 10, no. 3, pp. 58, 2021.
A. Alsarhan, M. Alauthman, E. Alshdaifat, A.-R. Al-Ghuwairi, and A. Al-Dubai, “Machine Learning-driven optimization for SVM-based intrusion detection system in vehicular ad hoc networks,” Journal of Ambient Intelligence and Humanized Computing, pp. 1-10, 2021.
Sharma, V. . (2022). Unique Functors of Everywhere Connected Homomorphisms and the Countability of Groups. International Journal on Recent Trends in Life Science and Mathematics, 9(2), 01–09. https://doi.org/10.17762/ijlsm.v9i2.130
P. Hadem, D. K. Saikia, and S. Moulik, “An SDN-based intrusion detection system using SVM with selective logging for IP traceback,” Computer Networks, vol. 191, pp. 108015, 2021.
R. O. Ogundokun, S. Misra, A. O. Bajeh, U. O. Okoro, and R. Ahuja, "An Integrated IDS Using ICA-Based Feature Selection and SVM Classification Method," Illumination of Artificial Intelligence in Cybersecurity and Forensics, pp. 255-271: Springer, 2022.
J. Gu, and S. Lu, “An effective intrusion detection approach using SVM with naïve Bayes feature embedding,” Computers & Security, vol. 103, pp. 102158, 2021.
S. Seniaray, and R. Jindal, "Machine Learning-Based Network Intrusion Detection System," Computer Networks and Inventive Communication Technologies, pp. 175-187: Springer, 2022.
T. Daniya, K. S. Kumar, B. S. Kumar, and C. S. Kolli, “A survey on anomaly based intrusion detection system,” Materials Today: Proceedings, 2021.
Pawan Kumar Tiwari, Mukesh Kumar Yadav, R. K. G. A. . (2022). Design Simulation and Review of Solar PV Power Forecasting Using Computing Techniques. International Journal on Recent Technologies in Mechanical and Electrical Engineering, 9(5), 18–27. https://doi.org/10.17762/ijrmee.v9i5.370
P. K. Keserwani, M. C. Govil, and E. S. Pilli, “An effective NIDS framework based on a comprehensive survey of feature optimization and classification techniques,” Neural Computing and Applications, pp. 1-21, 2021.
A. Drewek-Ossowicka, M. Pietrołaj, and J. Rumiński, “A survey of neural networks usage for intrusion detection systems,” Journal of Ambient Intelligence and Humanized Computing, vol. 12, no. 1, pp. 497-514, 2021.
T. Jafarian, M. Masdari, A. Ghaffari, and K. Majidzadeh, “A survey and classification of the security anomaly detection mechanisms in software defined networks,” Cluster Computing, vol. 24, no. 2, pp. 1235-1253, 2021.
I. Tomić, and J. A. McCann, “A survey of potential security issues in existing wireless sensor network protocols,” IEEE Internet of Things Journal, vol. 4, no. 6, pp. 1910-1923, 2017.
H. Radhappa, L. Pan, J. Xi Zheng, and S. Wen, “Practical overview of security issues in wireless sensor network applications,” International journal of computers and applications, vol. 40, no. 4, pp. 202-213, 2018.
R. A. Alshinina, and K. M. Elleithy, “A highly accurate deep learning based approach for developing wireless sensor network middleware,” IEEE Access, vol. 6, pp. 29885-29898, 2018.
B. Ahmad, W. Jian, Z. A. Ali, S. Tanvir, and M. Khan, “Hybrid anomaly detection by using clustering for wireless sensor network,” Wireless Personal Communications, vol. 106, no. 4, pp. 1841-1853, 2019.
M. Safaldin, M. Otair, and L. Abualigah, “Improved binary gray wolf optimizer and SVM for intrusion detection system in wireless sensor networks,” Journal of ambient intelligence and humanized computing, vol. 12, no. 2, pp. 1559-1576, 2021.
M. Frei, C. Deb, R. Stadler, Z. Nagy, and A. Schlueter, “Wireless sensor network for estimating building performance,” Automation in Construction, vol. 111, pp. 103043, 2020.
I. Batra, S. Verma, and M. Alazab, “A lightweight IoT‐based security framework for inventory automation using wireless sensor network,” International Journal of Communication Systems, vol. 33, no. 4, pp. e4228, 2020.
H. Chen, C. Meng, Z. Shan, Z. Fu, and B. K. Bhargava, “A novel Low-rate Denial of Service attack detection approach in ZigBee wireless sensor network by combining Hilbert-Huang Transformation and Trust Evaluation,” IEEE Access, vol. 7, pp. 32853-32866, 2019.
J. Hu, D. Ma, C. Liu, Z. Shi, H. Yan, and C. Hu, “Network security situation prediction based on MR-SVM,” IEEE Access, vol. 7, pp. 130937-130945, 2019.
I. Abrar, Z. Ayub, F. Masoodi, and A. M. Bamhdi, "A machine learning approach for intrusion detection system on NSL-KDD dataset." pp. 919-924.
R. R. Guimaraes, L. A. Passos, R. Holanda Filho, V. H. C. de Albuquerque, J. J. Rodrigues, M. M. Komarov, and J. P. Papa, “Intelligent network security monitoring based on optimum-path forest clustering,” Ieee Network, vol. 33, no. 2, pp. 126-131, 2018.
S. Suthaharan, M. Alzahrani, S. Rajasegarar, C. Leckie, and M. Palaniswami, "Labelled data collection for anomaly detection in wireless sensor networks." pp. 269-274.
J. Liu, B. Kantarci, and C. Adams, "Machine learning-driven intrusion detection for Contiki-NG-based IoT networks exposed to NSL-KDD dataset." pp. 25-30.
L. Gnanaprasanambikai, and N. Munusamy, “Data pre-processing and classification for traffic anomaly intrusion detection using nslkdd dataset,” Cybernetics and Information Technologies, vol. 18, no. 3, pp. 111-119, 2018.
D. Hemanand, D. S. Jayalakshmi, U. Ghosh, A. Balasundaram, P. Vijayakumar and P. K. Sharma, "Enabling Sustainable Energy for Smart Environment Using 5G Wireless Communication and Internet of Things," in IEEE Wireless Communications, vol. 28, no. 6, pp. 56-61, December 2021, doi: 10.1109/MWC.013.2100158.
D. S. Jayalakshmi, D. Hemanand, G. Muthu Kumar, M. Madhu Rani, "An Efficient Route Failure Detection Mechanism with Energy Efficient Routing (EER) Protocol in MANET", International Journal of Computer Network and Information Security(IJCNIS), Vol.13, No.2, pp.16-28, 2021. DOI: 10.5815/ijcnis.2021.02.02
Anusha, D. J. ., R. . Anandan, and P. V. . Krishna. “Modified Context Aware Middleware Architecture for Precision Agriculture”. International Journal on Recent and Innovation Trends in Computing and Communication, vol. 10, no. 7, July 2022, pp. 112-20, doi:10.17762/ijritcc.v10i7.5635.
Gopalakrishnan Subburayalu, Hemanand Duraivelu, Arun Prasath Raveendran, Rajesh Arunachalam, Deepika Kongara & Chitra Thangavel (2021): Cluster Based Malicious Node Detection System for Mobile Ad-Hoc Network Using ANFIS Classifier, Journal of Applied Security Research, DOI: 10.1080/19361610.2021.2002118
Linda R. Musser. (2020). Older Engineering Books are Open Educational Resources. Journal of Online Engineering Education, 11(2), 08–10. Retrieved from http://onlineengineeringeducation.com/index.php/joee/article/view/41
K. Selvakumar, M. Karuppiah, L. SaiRamesh, S. H. Islam, M. M. Hassan, G. Fortino, and K.-K. R. Choo, “Intelligent temporal classification and fuzzy rough set-based feature selection algorithm for intrusion detection system in WSNs,” Information Sciences, vol. 497, pp. 77-90, 2019.
P. Mohan Kumar & S. Gopalakrishnan (2016) Security Enhancement for Mobile Ad Hoc Network Using Region Splitting Technique, Journal of Applied Security Research, 11:2, 185-198, DOI: 10.1080/19361610.2016.1137204
Gopalakrishnan, S. and Kumar, P. (2016) Performance Analysis of Malicious Node Detection and Elimination Using Clustering Approach on MANET. Circuits and Systems, 7, 748-758. doi: 10.4236/cs.2016.76064.
Kumar, S., Gornale, S. S., Siddalingappa, R., & Mane, A. (2022). Gender Classification Based on Online Signature Features using Machine Learning Techniques. International Journal of Intelligent Systems and Applications in Engineering, 10(2), 260–268. Retrieved from https://ijisae.org/index.php/IJISAE/article/view/2020
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





