A Comprehensive Review of Hashing Algorithm Optimization for IoT Devices
Keywords:
Internet of Things, IoT, IoT Architecture Layers, hash, hashing, SHA, lightweight, optimized, optimization, optimizingAbstract
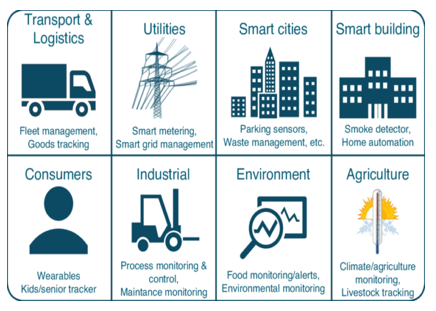
The Internet of Things (IoT) has grown dramatically in recent years, it is due to its big impact on people's daily life in critical applications like healthcare, smart homes, smart cities, and smart everything. It also attracts industries and researchers to work on this technology. IoT devices are susceptible to be compromised because of their network capacities, very low computing power, limited battery life, and data storage. The biggest obstacle to the adoption of IoT systems has been recognized as the requirement for lightweight and energy-efficient security solutions to secure smart devices and stored data. In this paper we have reviewed fourty five papers that are related to IoT hashing algorithms and its optimizations, and the papers were published from 2018 and 2022. The papers were then filtered and analyzed. After filtration process, fourteen papers were removed from the list, since they were not totally pertinent to the problem and thirty one papers left for analysis. Among these papers. Among of these thirty one papers, eighteen studies (58%) are focusing on Application layer security, more specifically they focused on Authentication in IoT System.
Downloads
References
Kairaldeen, A. R.; Abdullah, N. F.; Abu-Samah, A.; Nordin, R., Data integrity time optimization of a blockchain IoT smart home network using different consensus and hash algorithms. Wireless Communications and Mobile Computing 2021, 2021, 1-23.
Jebranea, J.; Lazaara, S., A performance comparison of lightweight cryptographic algorithms suitable for IoT transmissions. Gen. Lett. Math 2021, 10 (2), 46-53.
Dhanda, S. S.; Singh, B.; Jindal, P., Lightweight cryptography: a solution to secure IoT. Wireless Personal Communications 2020, 112, 1947-1980.
Hussien, N.; Ajlan, I.; Firdhous, M. M.; Alrikabi, H., Smart shopping system with RFID technology based on internet of things. 2020.
Diwan, S. A., Dynamic Lightweight Mechanism for Security and Performance in Internet of Things. International Journal of Interactive Mobile Technologies 2022, 16 (10).
Ma, J.; Sang, Y.; Zhang, Y.; Xu, X.; Feng, B.; Zeng, Y. In An Adaptive Ensembled Neural Network-Based Approach to IoT Device Identification, Collaborative Computing: Networking, Applications and Worksharing: 18th EAI International Conference, CollaborateCom 2022, Hangzhou, China, October 15-16, 2022, Proceedings, Part II, Springer: 2023; pp 214-230.
Shantha, R. M. J.; Mahender, K.; Jenifer, A. J. M.; Prasanth, A. In Security analysis of hybrid one time password generation algorithm for IoT data, AIP Conference Proceedings, AIP Publishing LLC: 2022; p 030021.
Reyna, A.; Martín, C.; Chen, J.; Soler, E.; Díaz, M., On blockchain and its integration with IoT. Challenges and opportunities. Future generation computer systems 2018, 88, 173-190.
Alfrhan, A.; Moulahi, T.; Alabdulatif, A., Comparative study on hash functions for lightweight blockchain in Internet of Things (IoT). Blockchain: Research and Applications 2021, 2 (4), 100036.
Denysiuka, D.; , T. S.; and Mariia Kapustiana, Proof of Stake And Proof of Work Approach for Malware Detection Technologies. CEUR Workshop Proceedings 2022, 3156.
Schiller, E.; Aidoo, A.; Fuhrer, J.; Stahl, J.; Ziörjen, M.; Stiller, B., Landscape of IoT security. Computer Science Review 2022, 44, 100467.
Alphonse, A. S.; Priya, E. D.; Kowsigan, M., Review of Machine Learning Techniques Used for Intrusion and Malware Detection in WSNs and IoT Devices. Design and Development of Efficient Energy Systems 2022, 57-65.
Haji, S. H.; Ameen, S. Y., Attack and anomaly detection in iot networks using machine learning techniques: A review. Asian journal of research in computer science 2021, 9 (2), 30-46.
Aggarwal, V. K.; Sharma, N.; Kaushik, I.; Bhushan, B. In Integration of Blockchain and IoT (B-IoT): Architecture, Solutions, & Future Research Direction, IOP Conference Series: Materials Science and Engineering, IOP Publishing: 2021; p 012103.
Alshahrani, H. M., Coll-iot: A collaborative intruder detection system for internet of things devices. Electronics 2021, 10 (7), 848.
Sikder, A. K.; Petracca, G.; Aksu, H.; Jaeger, T.; Uluagac, A. S., A survey on sensor-based threats and attacks to smart devices and applications. IEEE Communications Surveys & Tutorials 2021, 23 (2), 1125-1159.
Alhammadi, N. A. M.; Zaboon, K. H., A Review of IoT Applications, Attacks and Its Recent Defense Methods. Journal of Global Scientific Research 2022, 7 (3), 2128-2134.
Janani, K.; Ramamoorthy, S. In Iot security and privacy using deep learning model: a review, 2021 International conference on intelligent technologies (CONIT), IEEE: 2021; pp 1-6.
Lata, N.; Kumar, R., Security in Internet of Things (IoT): Challenges and Models. Mathematical Statistician and Engineering Applications 2022, 71 (2), 75–81-75–81.
Leloglu, E., A review of security concerns in Internet of Things. Journal of Computer and Communications 2016, 5 (1), 121-136.
Driss, M.; Hasan, D.; Boulila, W.; Ahmad, J., Microservices in IoT security: current solutions, research challenges, and future directions. Procedia Computer Science 2021, 192, 2385-2395.
Anuradha, M.; Jayasankar, T.; Prakash, N.; Sikkandar, M. Y.; Hemalakshmi, G.; Bharatiraja, C.; Britto, A. S. F., IoT enabled cancer prediction system to enhance the authentication and security using cloud computing. Microprocessors and Microsystems 2021, 80, 103301.
Cheng, H.; Dinu, D.; Großschädl, J. In Efficient implementation of the SHA-512 hash function for 8-bit AVR microcontrollers, Innovative Security Solutions for Information Technology and Communications: 11th International Conference, SecITC 2018, Bucharest, Romania, November 8–9, 2018, Revised Selected Papers 11, Springer: 2019; pp 273-287.
Dammak, M.; Boudia, O. R. M.; Messous, M. A.; Senouci, S. M.; Gransart, C. In Token-based lightweight authentication to secure IoT networks, 2019 16th IEEE Annual Consumer Communications & Networking Conference (CCNC), IEEE: 2019; pp 1-4.
Agrawal, M.; Zhou, J.; Chang, D., A survey on lightweight authenticated encryption and challenges for securing industrial IoT. Security and Privacy Trends in the Industrial Internet of Things 2019, 71-94.
Aghili, S. F.; Mala, H.; Kaliyar, P.; Conti, M., SecLAP: Secure and lightweight RFID authentication protocol for Medical IoT. Future Generation Computer Systems 2019, 101, 621-634.
Ahmed, A. A.; Ahmed, W. A., An effective multifactor authentication mechanism based on combiners of hash function over internet of things. Sensors 2019, 19 (17), 3663.
Dwivedi, A. D.; Malina, L.; Dzurenda, P.; Srivastava, G. In Optimized blockchain model for internet of things based healthcare applications, 2019 42nd international conference on telecommunications and signal processing (TSP), IEEE: 2019; pp 135-139.
Ostad-Sharif, A.; Arshad, H.; Nikooghadam, M.; Abbasinezhad-Mood, D., Three party secure data transmission in IoT networks through design of a lightweight authenticated key agreement scheme. Future Generation Computer Systems 2019, 100, 882-892.
Noura, H. N.; Melki, R.; Chehab, A. In Secure and lightweight mutual multi-factor authentication for IoT communication systems, 2019 IEEE 90th Vehicular Technology Conference (VTC2019-Fall), IEEE: 2019; pp 1-7.
Gupta, D. N.; Kumar, R., Lightweight cryptography: an IoT perspective. Trivium 2019, 80 (1), 2580.
Gunathilake, N. A.; Buchanan, W. J.; Asif, R. In Next generation lightweight cryptography for smart IoT devices:: implementation, challenges and applications, 2019 IEEE 5th World Forum on Internet of Things (WF-IoT), IEEE: 2019; pp 707-710.
Paliwal, S., Hash-based conditional privacy preserving authentication and key exchange protocol suitable for industrial internet of things. IEEE Access 2019, 7, 136073-136093.
Shah, A.; Engineer, M. In A survey of lightweight cryptographic algorithms for iot-based applications, Smart Innovations in Communication and Computational Sciences: Proceedings of ICSICCS-2018, Springer: 2019; pp 283-293.
Liu, Z.; Guo, C.; Wang, B., A physically secure, lightweight three-factor and anonymous user authentication protocol for IoT. IEEE Access 2020, 8, 195914-195928.
Melki, R.; Noura, H. N.; Chehab, A., Lightweight multi-factor mutual authentication protocol for IoT devices. International Journal of Information Security 2020, 19, 679-694.
Wu, P.; Xiao, F.; Huang, H.; Sha, C.; Yu, S., Adaptive and extensible energy supply mechanism for UAVs-aided wireless-powered Internet of Things. IEEE Internet of Things Journal 2020, 7 (9), 9201-9213.
Hossain, M.; Hasan, R., P-hip: A lightweight and privacy-aware host identity protocol for internet of things. IEEE Internet of Things Journal 2020, 8 (1), 555-571.
Choudhary, K.; Gaba, G. S.; Butun, I.; Kumar, P., Make-it—A lightweight mutual authentication and key exchange protocol for industrial internet of things. Sensors 2020, 20 (18), 5166.
Sha, K.; Yang, T. A.; Wei, W.; Davari, S., A survey of edge computing-based designs for IoT security. Digital Communications and Networks 2020, 6 (2), 195-202.
Suhail, S.; Hussain, R.; Khan, A.; Hong, C. S., On the role of hash-based signatures in quantum-safe internet of things: Current solutions and future directions. IEEE Internet of Things Journal 2020, 8 (1), 1-17.
Hammi, B.; Fayad, A.; Khatoun, R.; Zeadally, S.; Begriche, Y., A lightweight ECC-based authentication scheme for Internet of Things (IoT). IEEE Systems Journal 2020, 14 (3), 3440-3450.
Al-Shatari, M. O. A.; Hussin, F. A.; Abd Aziz, A.; Witjaksono, G.; Tran, X.-T., FPGA-based lightweight hardware architecture of the PHOTON hash function for IoT edge devices. IEEE Access 2020, 8, 207610-207618.
Guruprakash, J.; Koppu, S., EC-ElGamal and Genetic algorithm-based enhancement for lightweight scalable blockchain in IoT domain. IEEE Access 2020, 8, 141269-141281.
Nabeel, N.; Habaebi, M. H.; Islam, M. R., Security analysis of LNMNT-lightweight crypto hash function for IoT. IEEE Access 2021, 9, 165754-165765.
Gupta, D. N.; Kumar, R. In Sponge based lightweight cryptographic hash functions for IoT applications, 2021 International Conference on Intelligent Technologies (CONIT), IEEE: 2021; pp 1-5.
Pohrmen, F. H.; Saha, G. In Lightbc: A lightweight hash-based blockchain for the secured internet of things, International Conference on Innovative Computing and Communications: Proceedings of ICICC 2020, Volume 1, Springer: 2021; pp 811-819.
Parmar, M., Hashing based Data Transaction and Optimized Storage for IoT Applications. Turkish Journal of Computer and Mathematics Education (TURCOMAT) 2021, 12 (5), 1206-1215.
Idriss, T. A.; Idriss, H. A.; Bayoumi, M. A., A lightweight PUF-based authentication protocol using secret pattern recognition for constrained IoT devices. IEEE Access 2021, 9, 80546-80558.
Jan, M. A.; Khan, F.; Mastorakis, S.; Adil, M.; Akbar, A.; Stergiou, N., LightIoT: Lightweight and secure communication for energy-efficient IoT in health informatics. IEEE transactions on green communications and networking 2021, 5 (3), 1202-1211.
Choudhury, H., HashXor: A lightweight scheme for identity privacy of IoT devices in 5G mobile network. Computer Networks 2021, 186, 107753.
Chhaybi, A.; Lazaar, S., Definition of a lightweight cryptographic solution to secure health data on IoT and cloud. Gen. Lett. Math 2021, 10 (2), 54-60.
Kumar, A.; Gupta, D. N.; Kumar, R. In Hash Constructions for CoAP under an IoT Environment, 2021 International Conference on Smart Generation Computing, Communication and Networking (SMART GENCON), IEEE: 2021; pp 1-7.
Sadhukhan, D.; Ray, S.; Biswas, G.; Khan, M. K.; Dasgupta, M., A lightweight remote user authentication scheme for IoT communication using elliptic curve cryptography. The Journal of Supercomputing 2021, 77, 1114-1151.
Adil, M.; Jan, M. A.; Mastorakis, S.; Song, H.; Jadoon, M. M.; Abbas, S.; Farouk, A., Hash-MAC-DSDV: Mutual Authentication for Intelligent IoT-Based Cyber–Physical Systems. IEEE Internet of Things Journal 2021, 9 (22), 22173-22183.
Mohammad, A.; Al-Refai, H.; Alawneh, A. A., User Authentication and Authorization Framework in IoT Protocols. Computers 2022, 11 (10), 147.
Deebak, B.; Memon, F. H.; Cheng, X.; Dev, K.; Hu, J.; Khowaja, S. A.; Qureshi, N. M. F.; Choi, K. H., Seamless privacy-preservation and authentication framework for IoT-enabled smart eHealth systems. Sustainable Cities and Society 2022, 80, 103661.
Moradi, M.; Moradkhani, M.; Tavakoli, M. B., Security-level improvement of IoT-based systems using biometric features. Wireless Communications and Mobile Computing 2022, 2022, 1-15.
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





