A Multi-Cast Policy Management Process for Improved Network Security with the Group-Oriented Applications
Keywords:
Group-oriented communication, Multi-cast policy, Policy management, polynomial, Communication cost, Storage CostAbstract
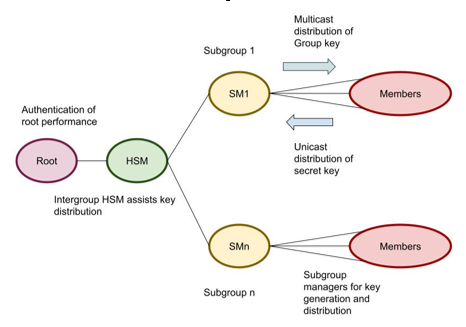
The increased Internet utilization leads to emerging group-basedapplications such as military, healthcare, online collaboration, video conferencing and so. However, in the group-oriented application resources are secured through a constraint network. The promising multi-cast communication group-oriented communication model exhibits reduced bandwidth with the different decentralized group key management such as the decentralized group key framework. In this paper, proposed a Multicast Polynomial Key Distribution Scheme (MPKD)model with acentralized and decentralized key management framework. The proposed MPKD model comprises of the three process such as generation of key, distribution of key and refreshment of key. The proposed MPKD mode uses the logical key tree structure with the computation of the polynomial in the key generation process. The performance analysis is based on the structure protocol with the key distribution in the centralized framework model. The performance of the proposed MPKD model is comparatively examined with the conventional OFT, SKD and MUKD model. The analysis of the results expressed that proposed model ~2% - 4% reduces the communication and storage cost. The storage cost of the existing model exhibits the value of maximal 63 but the proposed MPKD model achieves 34 for the user count of 32. Similarly, the communication and storage cost is minimal for the unicast and multicast communication.
Downloads
References
Ali, R. F., Dominic, P. D. D., Ali, S. E. A., Rehman, M., & Sohail, A. (2021). Information security behavior and information security policy compliance: A systematic literature review for identifying the transformation process from noncompliance to compliance. Applied Sciences, 11(8), 3383.
Blazhevska, K. V. (2022). The Social Security Policy of the Republic of North Macedonia: Reform Process, Opportunities and Perspectives. In Social Security in the Balkans–Volume 2 (pp. 13-33). Brill.
Figueiredo, S. O. D., Sincorá, L. A., Leite, M. C. D. O., & Brandão, M. M. (2021). Determinants of crime control in public security policy management. Revista de Administração Pública, 55, 438-458.
Dong, K., Ali, R. F., Dominic, P. D. D., & Ali, S. E. A. (2021). The effect of organizational information security climate on information security policy compliance: The mediating effect of social bonding towards healthcare nurses. Sustainability, 13(5), 2800.
Lingga, P., Kim, J., Bartolome, J. D. I., & Jeong, J. (2021, October). Automatic Data Model Mapper for Security Policy Translation in Interface to Network Security Functions Framework. In 2021 International Conference on Information and Communication Technology Convergence (ICTC) (pp. 882-887). IEEE.
McLeod, A., & Dolezel, D. (2022). Information security policy non-compliance: Can capitulation theory explain user behaviors?. Computers & Security, 112, 102526.
Wong, W. P., Tan, K. H., Chuah, S. H. W., Tseng, M. L., Wong, K. Y., & Ahmad, S. (2020). Information sharing and the bane of information leakage: a multigroup analysis of contract versus noncontract. Journal of Enterprise Information Management, 34(1), 28-53.
Jaeger, L., Eckhardt, A., & Kroenung, J. (2021). The role of deterrability for the effect of multi-level sanctions on information security policy compliance: Results of a multigroup analysis. Information & Management, 58(3), 103318.
Flores, W. R., Antonsen, E., & Ekstedt, M. (2014). Information security knowledge sharing in organizations: Investigating the effect of behavioral information security governance and national culture. Computers & security, 43, 90-110.
Yazdanmehr, A., Wang, J., & Yang, Z. (2020). Peers matter: The moderating role of social influence on information security policy compliance. Information Systems Journal, 30(5), 791-844.
Muller, S. R., & Lind, M. L. (2020). Factors in information assurance professionals' intentions to adhere to information security policies. International Journal of Systems and Software Security and Protection (IJSSSP), 11(1), 17-32.
Herath, T., & Rao, H. R. (2009). Protection motivation and deterrence: a framework for security policy compliance in organisations. European Journal of information systems, 18(2), 106-125.
Chen, X., Wu, D., Chen, L., & Teng, J. K. (2018). Sanction severity and employees’ information security policy compliance: Investigating mediating, moderating, and control variables. Information & Management, 55(8), 1049-1060.
Chen, X., Wu, D., Chen, L., & Teng, J. K. (2018). Sanction severity and employees’ information security policy compliance: Investigating mediating, moderating, and control variables. Information & Management, 55(8), 1049-1060.
Alshare, K. A., Lane, P. L., & Lane, M. R. (2018). Information security policy compliance: a higher education case study. Information & Computer Security.
Brown, D. A. (2017). Examining the Behavioral Intention of Individuals' Compliance with Information Security Policies (Doctoral dissertation, Walden University).
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Nanang Yusroni, Dhruv Galgotia, Aniruddha Bodhankar, Hendy Tannady, H. Mary Henrietta, Akash Kumar Bhaga

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





