Algorithm for Digital Image Encryption Using Multiple Hill Ciphers, a Unimodular Matrix, and a Logistic Map
Keywords:
image encryption, multiple hill ciphers, unimodular matrix, logistic mapAbstract
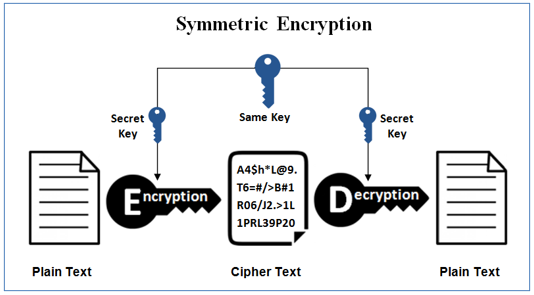
The security of digital images is becoming increasingly important due to the widespread use of image transmission through networks. Therefore, encryption is necessary to protect the confidentiality and integrity of digital images. In this paper, a new digital image encryption algorithm is proposed by combining multiple Hill ciphers, unimodular matrix, and logistic map. The proposed algorithm can improve the security of the image encryption process by introducing multiple encryption layers. The unimodular matrix is used to shuffle the image pixels and the logistic map is used to generate the encryption keys. The performance of the proposed algorithm is evaluated by applying it to various types of digital images. The experimental results show that the proposed algorithm can achieve high-level security. Moreover, the proposed algorithm has a faster encryption time compared to other existing image encryption algorithms. Therefore, it is a promising algorithm for digital image encryption applications that require high security and fast processing time.
Downloads
References
I. B. Muktyas, Sulistiawati, and S. Arifin, “Digital image encryption algorithm through unimodular matrix and logistic map using Python,” in AIP Conference Proceedings, 2021, vol. 2331. doi: 10.1063/5.0041653.
A. J. Akinboboye, A. S. Oluwole, O. Akinsanmi, and A. E. Amoran, “Cryptographic Algorithms for IoT Privacy: A Technical Review,” Int. J. Eng. Trends Technol., vol. 70, no. 8, pp. 185–193, 2022, doi: 10.14445/22315381/IJETT-V70I8P219.
N. Faizal, S. Sharan, P. S. Nair, and D. S. Sankar, Securing Color Image Using Combined Elliptic Curve Crypto-System and Hill Cipher Encryption Along with Least Significant Bit - Steganography, vol. 98. 2020. doi: 10.1007/978-3-030-33846-6_40.
S. Ventures, “APA ITU ENKRIPSI ASIMETRIS & SIMETRIS?” https://www.websiterating.com/id/vpn/glossary/what-is-asymmetric-symmetric-encryption/ (accessed Feb. 25, 2023).
M. Fadlan, Haryansyah, and Rosmini, “Three Layer Encryption Protocol: An Approach of Super Encryption Algorithm,” in 3rd International Conference on Cybernetics and Intelligent Systems, ICORIS 2021, 2021. doi: 10.1109/ICORIS52787.2021.9649574.
P. N. Lone, D. Singh, V. Stoffová, D. C. Mishra, U. H. Mir, and N. Kumar, “Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher,” Mathematics, vol. 10, no. 20, 2022, doi: 10.3390/math10203878.
S. M. Zia Sardar, Aaron Arellano, “Cryptographic Implementations: Hardware vs. Software,” Electronic Design, 2020. https://www.electronicdesign.com/technologies/embedded/article/21132412/maxim-integrated-cryptographic-implementations-hardware-vs-software
E. A. Jameel and S. A. Fadhel, “Digital Image Encryption Techniques: Article Review,” Tech. Rom. J. Appl. Sci. Technol., vol. 4, no. 2, pp. 24–35, 2022, doi: 10.47577/technium.v4i2.6026.
J. R. Paragas, “An Enhanced Cryptographic Algorithm in Securing Healthcare Medical Records,” in Proceeding - 2020 3rd International Conference on Vocational Education and Electrical Engineering: Strengthening the framework of Society 5.0 through Innovations in Education, Electrical, Engineering and Informatics Engineering, ICVEE 2020, 2020. doi: 10.1109/ICVEE50212.2020.9243228.
P. N. Lone and D. Singh, “Application of algebra and chaos theory in security of color images,” Optik (Stuttg)., vol. 218, 2020, doi: 10.1016/j.ijleo.2020.165155.
D. Nofriansyah et al., “A New Image Encryption Technique Combining Hill Cipher Method, Morse Code and Least Significant Bit Algorithm,” in Journal of Physics: Conference Series, 2018, vol. 954, no. 1. doi: 10.1088/1742-6596/954/1/012003.
F. Serzhenko, “JPEG2000 vs JPEG vs PNG,” Fastvideo, 2020. https://www.fastcompression.com/blog/jpeg-j2k-png-review.htm
A. Laurinavicius et al., “Digital image analysis in pathology: benefits and obligation,” Anal. Cell. Pathol., vol. 35, no. 2, pp. 75–78, 2012.
S. Arifin, F. I. Kurniadi, I. G. A. Yudistira, R. Nariswari, N. P. Murnaka, and I. B. Muktyas, “Image Encryption Algorithm Through Hill Cipher, Shift 128 Cipher, and Logistic Map Using Python,” in 2022 3rd International Conference on Artificial Intelligence and Data Sciences: Championing Innovations in Artificial Intelligence and Data Sciences for Sustainable Future, AiDAS 2022 - Proceedings, 2022, pp. 221–226. doi: 10.1109/AiDAS56890.2022.9918696.
M. Terras, Digital images for the information professional. Routledge, 2016.
S. Kanwal et al., “An Effective Color Image Encryption Based on Henon Map, Tent Chaotic Map, and Orthogonal Matrices,” Sensors, vol. 22, no. 12, 2022, doi: 10.3390/s22124359.
M. T. Suryadi, Y. Satria, and A. Hadidulqawi, “Implementation of the Gauss-Circle Map for encrypting and embedding simultaneously on digital image and digital text,” J. Phys. Conf. Ser., vol. 1821, no. 1, 2021, doi: 10.1088/1742-6596/1821/1/012037.
S. Arifin, I. B. Muktyas, P. W. Prasetyo, and A. A. Abdillah, “Unimodular matrix and bernoulli map on text encryption algorithm using python,” Al-Jabar J. Pendidik. Mat., vol. 12, no. 2, pp. 447–455, 2021.
S. Arifin and I. B. Muktyas, “Membangkitkan Suatu Matriks Unimodular Dengan Python,” J. Deriv. J. Mat. dan Pendidik. Mat., vol. 5, no. 2, pp. 1–10, 2018.
M. A. Lone and S. Qureshi, “Encryption scheme for RGB images using chaos and affine hill cipher technique,” Nonlinear Dyn., vol. 111, no. 6, pp. 5919–5939, 2023, doi: 10.1007/s11071-022-07995-2.
A. Kaur and S. Singh, “A hybrid technique of cryptography and watermarking for data encryption and decryption,” in 2016 4th International Conference on Parallel, Distributed and Grid Computing, PDGC 2016, 2016, pp. 351–356. doi: 10.1109/PDGC.2016.7913175.
J. F. Dooley, The machines take over: Computer cryptography, vol. 0, no. 9783319016. 2013. doi: 10.1007/978-3-319-01628-3_8.
P. Hernández-Lamas, B. Cabau-Anchuelo, Ó. de Castro-Cuartero, and J. Bernabéu-Larena, “Mobile Applications, Geolocation and Information Technologies for the Study and Communication of the Heritage Value of Public Works,” Sustainability, vol. 13, no. 4, p. 2083, 2021.
Z. E. Dawahdeh, S. N. Yaakob, and R. Razif bin Othman, “A new image encryption technique combining Elliptic Curve Cryptosystem with Hill Cipher,” J. King Saud Univ. - Comput. Inf. Sci., vol. 30, no. 3, pp. 349–355, 2018, doi: 10.1016/j.jksuci.2017.06.004.
M. Toorani and A. Falahati, “A secure variant of the hill cipher,” in Proceedings - IEEE Symposium on Computers and Communications, 2009, pp. 313–316. doi: 10.1109/ISCC.2009.5202241.
J. R. Paragas, A. M. Sison, and R. P. Medina, “A new variant of hill cipher algorithm using modified S-Box,” Int. J. Sci. Technol. Res., vol. 8, no. 10, pp. 615–619, 2019.
3rd International Conference on Smart Computing and Informatics, SCI 2018, vol. 159. 2020.
S. J. Gladwin and P. Lakshmi Gowthami, “Combined Cryptography and Steganography for Enhanced Security in Suboptimal Images,” in 2020 International Conference on Artificial Intelligence and Signal Processing, AISP 2020, 2020. doi: 10.1109/AISP48273.2020.9073306.
S. Kanwal, S. Inam, O. Cheikhrouhou, K. Mahnoor, A. Zaguia, and H. Hamam, “Analytic Study of a Novel Color Image Encryption Method Based on the Chaos System and Color Codes,” Complexity, vol. 2021, 2021, doi: 10.1155/2021/5499538.
R. Tuli, H. N. Soneji, and P. Churi, “PixAdapt: A novel approach to adaptive image encryption,” Chaos, Solitons and Fractals, vol. 164, 2022, doi: 10.1016/j.chaos.2022.112628.
S. Arifin, K. Tan, A. T. Ariani, S. Rosdiana, and M. N. Abdullah, “The Audio Encryption Approach uses a Unimodular Matrix and a Logistic Function,” Int. J. Emerg. Technol. Adv. Eng., vol. 13, no. 4, pp. 71–81, 2023.
T. E. Oliphant, “Python for scientific computing,” Comput. Sci. Eng., vol. 9, no. 3, pp. 10–20, 2007.
Python Software Foundation, “Python TM,” Python.org. https://www.python.org/ (accessed Feb. 15, 2023).
S. Hraoui, F. Gmira, M. F. Abbou, A. J. Oulidi, and A. Jarjar, “A New Cryptosystem of Color Image Using a Dynamic-Chaos Hill Cipher Algorithm,” Procedia Comput. Sci., vol. 148, pp. 399–408, 2019, doi: https://doi.org/10.1016/j.procs.2019.01.048.
DarwIn, “File:500px photo (68947463).jpeg,” WikimediaCommons, 2018. https://commons.wikimedia.org/wiki/File:500px_photo_(68947463).jpeg
H. Nasir, “A view of a sunrise from a countryside in Jhang, Punjab, Pakistan.,” WikimediaCommons, 2017. https://commons.wikimedia.org/wiki/Category:Green_landscapes#/media/File:A_view_of_a_sunrise_from_a_countryside_in_Jhang,_Punjab,_Pakistan.jpg
Downloads
Published
How to Cite
Issue
Section
License

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
All papers should be submitted electronically. All submitted manuscripts must be original work that is not under submission at another journal or under consideration for publication in another form, such as a monograph or chapter of a book. Authors of submitted papers are obligated not to submit their paper for publication elsewhere until an editorial decision is rendered on their submission. Further, authors of accepted papers are prohibited from publishing the results in other publications that appear before the paper is published in the Journal unless they receive approval for doing so from the Editor-In-Chief.
IJISAE open access articles are licensed under a Creative Commons Attribution-ShareAlike 4.0 International License. This license lets the audience to give appropriate credit, provide a link to the license, and indicate if changes were made and if they remix, transform, or build upon the material, they must distribute contributions under the same license as the original.





